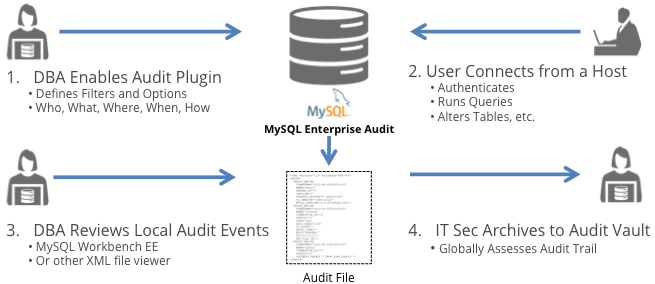
MySQL Enterprise Audit
MySQL Enterprise Audit provides an easy to use, policy-based auditing solution that helps organizations implement stronger security controls and satisfy regulatory compliance.
As more sensitive data is collected, stored and used online, database auditing becomes an essential component of any security strategy. To guard against the misuse of information, popular compliance regulations including HIPAA, Sarbanes-Oxley, and the PCI Data Security Standard require organizations to track access to information.
To meet these demands, organizations must be able to produce an audit trail of information to help track who does what to which piece of data. This includes login and logoff attempts, attempts to access a database or a table, changes to database schema and much more.
MySQL Enterprise Audit gives DBAs the tools they need to add auditing compliance to their new and existing applications by enabling them to:
- User Defined Custom Audit Log Events - Now you can add custom events to the MySQL Audit Log, providing added information related to SQL calls. For example, tracking numbers, help desk ticket references, or other application context.
- Encryption - Audit Files can now be encrypted using standard AES-256. These files can be shared and decrypted by external applications that have the encryption key.
- Compression - Using compression can Reduce audit storage by up to 10x. Files can be unzipped using standard tools.
- JSON Audit Data Format - Now you can decide between JSON or XML.
- Powerful Filtering to Protect Sensitive Data - Define what you audit using templates or design highly custom filters using simple JSON filter definition. Filter on connections, users, table access, access type, statement status (success/failure), query content, and more.
- Meet Regulatory compliance standards - Provide the data your organization and auditors need to be in compliance with requirements including PCI, HIPAA, FERPA, SOX and more.
- Achieve Security Goals through Comprehensive Auditing - Trust but verify DBA activity, prove your data’s validity and perform forensic analysis to investigate or discover data breaches.
- Easy Integration with Audit Vaults and Stores - Externally archive and analyze XML-based audit logs with ease using Oracle Audit Vault and other third party solutions including Splunk.
- Dynamic and Easy to Manage - Dynamically enable/disable audit stream, change filtering, and more with no downtime. Automatically rotate audit log files based on size.
- Low Overhead - Collects critical audit data without minimal performance impact. Use fine grain filtering to minimize audit log size and IO impact.
- Remove Sensitive Data - Enables removal of sensitive data from SQL Statements in the audit log.